The Connection, Inc Blog
It’s a symbol that we’ve all become familiar with in recent years: three horizontal lines, representing the menu of whatever application or website is currently in use. Sometimes appearing as three dots, this little icon can be surprisingly important for both the end user and the business using it… especially now that mobile devices are so commonly used for browsing (early this year, 64% of all website traffic was observed to come from these devices).
There are plenty of technical terms and solutions that, while heard of frequently enough, it may not be completely clear what they mean or refer to. A proxy server is an excellent example of such a solution. This week, we’ll examine this tech term and review how utilizing proxy servers can help your business.
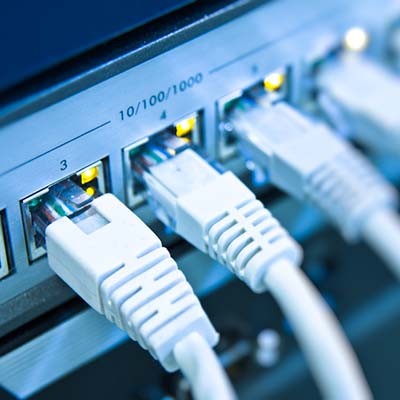
The Internet is a valuable tool that can be accessed through a wired connection and wirelessly via Wi-Fi, but the devices that offer these connections can be somewhat complicated and difficult to understand. If you don’t know which device does what, you’re in for a treat--today’s tech term will examine the differences between the modem and the router.
Before we get started, let’s get one thing out of the way; a router and a modem are two completely different things that are working toward the same end goal. The modem and router work in concert to make up what you know as a wireless network.
What Does the Modem Do?
A modem is the device that connects your local network to your Internet service provider. This also means that it’s the gateway to your Internet connection. It allows for constant connection to the Internet without any type of filtering.
What Does the Router Do?
The router is the device that bridges the gap between devices on your network and the Internet. This can be done either through a wired or a wireless network. Routers often feature security measures that can keep external threats from entering your infrastructure as well, but this is mostly on a fundamental level rather than a comprehensive one.
Sometimes you don’t even need a router to access the Internet, and you can instead rely on a wired connection directly to the modem. Ultimately, whether or not you need a router comes down to whether or not you have multiple mobile devices accessing the Internet.
Combination Modems and Routers
There’s usually an option to consolidate modems and routers into the same device. However, using a combination device like this can limit how much you can do with your network. You don’t have as much control and flexibility with your networking components as you may if you have a stand-alone modem and router.
Is your business in need of networking management? The Connection can help you work with your ISP to get the best equipment for your wireless network’s access. To learn more, reach out to us at (732) 291-5938.
The Internet has become an irreplaceable part of many business’ operations, which brings the thought into question of how much you rely on it for your daily duties. Technology has changed the way that the Internet works for the better, but there is one part of its operations that still lies at the heart of it: bandwidth.
In the context of the Internet, bandwidth is used to measure the volume of information per unit of time that a transmission medium can handle. Basically, the more bandwidth your connection has, the faster data can be transferred. Bandwidth is typically measured in seconds. You might remember seeing the specifics about your Internet connection in the form of megabits per second (like Mbps or Mb/s). Megabytes, usually abbreviated to MB, is not used for measuring bandwidth. For example, a connection that is advertised as 15 MB is, in reality, 1.875 Mbps due to there being eight bits in every byte.
Most Internet Service Providers, or ISPs, will market their packages at a certain megabit value, but this isn’t the best way to see just how much bandwidth your connection gets. To do this, you can use a speed tester such as the one at speedtest.net.
Perhaps the best analogy to describe bandwidth is plumbing. Imagine that data is water flowing through a pipe. As the amount of water increases, there isn’t as much room for water to flow through the pipe. If you find a larger pipe, more water can pass through at once. For more users that only take advantage of a couple of applications and a web browser, a small bandwidth connection might be enough, but streaming media can complicate these matters. Tech-savvy families and small businesses might find that smaller bandwidth connections are inadequate, as there isn’t enough room for the amount of data being used to be sent through the “pipe.” Larger businesses need a lot data, so it’s recommended that they acquire enterprise-level bandwidth to make up for the considerable increase in data being used.
Bandwidth is also used for various other functions for your business, including your website. You will generally have to pay for the amount of traffic that your website receives, but this isn’t always the case.
Did you learn anything during this week’s tech term? Let us know in the comments.
You may have heard technology professionals use the word “cache,” pronounced cash, in their day-to-day duties, but do you really know what it means? Generally, the context of this word is that users should “clear the cache,” but unless you know what that process entails, you won’t really understand what the cache does or why it’s used in this way. This week’s tech term is cache, so let’s see what hidden treasures this word yields.
Running a business sometimes requires attention to very minute details, and some things must be measured in order to achieve optimal efficiency. You’ve likely heard the terms bits and bytes used regarding data storage or transfer, but do you know what the difference is between them? Today’s tech term is dedicated to this explanation.
One of the first things you’ll notice when you go to buy a new computer is how much data the hard drive can store and how much random access memory (RAM) it contains. You might see numbers like 500GB or 2TB. The easiest way to explain this is by looking at the basics of data measurement. You can think of a bit as the smallest form of data measurement on a computer. Computers use binary math to showcase each potential digit as a bit. Each bit has a value of a 0 or 1. These bits are generated by the computer’s electrical current that activates the various internal components. These changes in voltage are used to transmit the bits, process calculations, and relay data across the network.
Here are some of the methods used during network message encoding:
- Wi-Fi carries bits using radio signals
- Ethernet connections carry bits using electric signals of varying voltages
- Fiber connections use pulses of light to carry bits
Ideally, the bits are encrypted so that they can’t be interpreted without permission.
On the other hand, the byte is a fixed sequence of bits. Technology today relies on organizing data into bytes to increase the speed and efficiency of data processing. Bits are often too small to measure data, which is why a byte is easier to use as the standard measurement.
The rate at which a computer network connection is measured is through time (bits per second), and today’s technology has advanced so far that it can transmit millions, or even billions, of bits per second (called megabits (Mbps) or gigabits (Gbps). The speed at which this data is transferred depends on the size of the file sizes or components transferring the data.
This is one of the reasons why gigabit network switches and other devices exist. If a device can support 1 Gbps, it transfers a single gigabit per second. Depending on your infrastructure, you might need to transfer more than this amount of data so that the network can operate smoothly. Other devices on your network will also play a major role in determining what your overall maximum speed is.
Breaking Down the Numbers
Since every byte is eight bits, you could safely assume that a kilobyte is 1,000 bytes, but you would be mistaken. Computers use binary systems, so your hard drives, memory, and bandwidth are all measured in powers of two. Thus, 2 ^ 10 equals 1,024, not 1,000. This makes looking at the specific numbers somewhat confusing for the average user.
If you look at everyday examples of this in practice, it becomes a little easier to understand and work with. Take a look at your IP address. This contains a string of 32 bits (or four bytes). An IP address with a value of 192.168.1.1 has values of 192, 168, 1, and 1 for each of its bytes. If you look at the encoding of this IP address, it would look like this:
11000000 10101000 00000001 000000001
This means that:
- 192 = 1100000
- 168 = 1010100
- 1 = 00000001
How to Convert Bits to Bytes (and Beyond)
If you ever need to convert bits to bytes or otherwise, here are the numbers.
- 8 bits = 1 byte
- 1,024 bytes = kilobyte
- 1,024 kilobytes = megabyte
- 1,024 megabytes = gigabyte
- 1,024 gigabytes = terabyte
If you want to convert four kilobytes into bits, you need to first convert the kilobytes to bytes (4 x 1,024) and then use that total (4,096) to convert to bits (8 x 4,096 = 32,768).
From a consumer standpoint, if you purchase a hard drive that has a terabyte of data, it’s real value is about 8 trillion bits. Hard drive manufacturers measure content by rounding down to 1,000 megabytes per gigabyte, even though most computers will use the 1,024 number. This is why when you purchase a new terabyte hard drive, you’ll notice that about 35 gigabytes aren’t immediately available. In the case of a workstation, the operating system will also consume a certain amount of data on the drive.
Did we answer some of your questions about computing and the specifics of bits vs bytes? Let us know in the comments what you would like to see covered in our tech term articles.
In some situations, competition is good for a business; and, for others, it can be terrible. As marketing, and specifically online marketing becomes more imperative for the success of every organization, all the content that is created for this purpose has to be managed. For this week’s technology term, we take a look at the different kinds of content management services (CMS) and what they do to make managing your organization’s content simpler.
What is a CMS?
A CMS is an application that stores content, provides easy editing options, and third-party integrations to get the most out of your content. It provides a central hub that allows anyone with access the ability to build, alter, and store content. Each type of application needs a strategy. There are two different CMS strategies that you have to be cognizant of:
- Web content management
- Enterprise content management
We’ll look at each strategy and describe why they are useful and how to choose the one right for you.
Web-Based Content Management System (WCMS)
If your organization has rolled out a website, chances are that you had a website creator build it. It uses a WCMS to create and manage all the content found on the website. Since your website is the central hub of your entire web marketing strategy, ensuring that you are getting the features and management capabilities that will allow you to get the most out of your efforts is important to the success of those endeavors. A WCMS provides these opportunities, and more than that, it offers people that don’t have any experience with the creation and management of websites options to do both with no prior training.
With marketing often, a day-by-day process, organizations need to be able to make changes to their websites on the fly. By using a Web-based CMS, you will be able to quickly create, edit, and publish content that is relevant to your current business initiatives while also integrating forms, forums, and even social media in order to get the best degree of customer and prospect engagement.
Some titles include: WordPress, Joomla, and Drupal.
Enterprise Content Management System
Enterprise content management is a bit different, but it does largely the same thing. It provides a construct to manage content in an online environment and gives everyone inside an organization a deep and functional repository of information that’s easy to access and manage. Some of the ways that businesses will use this system include:
- Improving security by managing access to organizational content.
- Making files easy to access and searchable, boosting an organization’s collaboration capabilities.
- Centralizing all organizational content.
- Incorporating a document management system (DMS) to further build a digital content storage platform.
- Creating and storing templates to improve workflow efficiency.
To remain competitive in business today, businesses need to have access to information, and control over that information. The enterprise content management system does exactly that. Since management of content is management of data, having a system in place that allows for comprehensive access to all of an organization’s content works to make that business more profitable.
Some titles include: HP Distributed Workflow, IBM ECM, Oracle WebCenter Content.
At The Connection, we can provide more information about content management systems, and what software titles will work best for your situation. Call us today at (732) 291-5938 to learn more.
Sometimes it can be hard to diagnose a problem with your PC. While it might not be something system-breaking, it’s still important to find the root of an issue before it becomes a major problem. One of the best ways to diagnose an issue with your computer is by logging in using Safe Mode. We’ll talk about when and how you can use Safe Mode to your computer’s benefit.
Computers use quite a lot of different types of protocol to function. In particular, the Internet takes advantage of protocol to a great degree. You might recognize terms like Hypertext Transfer Protocol Secure, Transmission Control Protocol/Internet Protocol, File Transfer Protocol, Internet Message Protocol, and Post Office Protocol. But what exactly is protocol, and why is it important?
It is no secret that security is an absolutely crucial part of computing in the modern era. Data can very fairly be called the most valuable currency today, which means it needs to be protected. One way to do this is through the use of encryption keys. In this Tech Term, we’ll go over how these keys can protect your data, and how they do so.
The term “hacker” is possibly one of the best-known technology-related terms there is, thanks to popular culture. Properties like The Girl with the Dragon Tattoo and the Die Hard franchise have given the layman a distinct impression of what a hacker is. Unfortunately, this impression isn’t always accurate. Here, we’ll discuss what real-life hackers are like, and the different varieties there are.
You open a lot of files and folders during your duties around the office, but some of them might seem a little different from others. These files are marked as “read-only.” What is the significance behind these files, and what does this marking mean? Find out in this week’s tech term.
Reading into Read-Only
Read-only is an attribute that is stored alongside the file that keeps users from doing more than just reading the contents. This attribute blocks users from changing or deleting the files, which might lead you to believe that “read-only” means that the file is extremely important.
Other files that aren’t necessarily important can also be assigned the read-only attribute. A folder could take advantage of read-only, preventing its contents from being altered unless the attribute is removed from the folder. External storage media can also use this attribute to keep others from messing around with your flash drives and SD cards. Even the CD-ROM, those relics of the past, took advantage of read-only technology (the acronym actually stands for Compact Disk Read-Only Memory), preventing users from overwriting the data stored on the disk.
Why Are Documents Marked This Way?
There are several reasons why a file or folder might be marked as read-only, but the primary one you’ll see is that these files or folders aren’t meant to be seen in the first place. These files are meant to be protected from being changed, as they are often critical files for a computer’s hardware and software. Certain files need to be in specific locations, as well as contain specific information. If the file is altered, the computer simply won’t work properly.
In essence, this functionality is programmed in so that users can’t accidentally disable their computers by deleting the wrong files. Besides, these files are more or less hidden from view anyway, meaning that users wouldn’t be able to delete them in the first place.
You can mark a file as read-only yourself as well, which you can do by accessing the properties. This could be helpful if your business wants to make a certain file available for all to see but without actually giving permissions to edit the file (like your employee handbook). What are some other uses you can think of for a read-only file? Let us know in the comments.
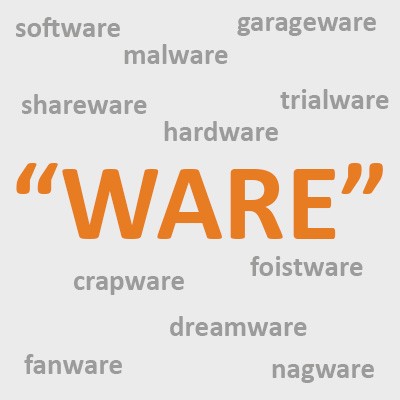
When you’re talking about something to do with a computer, you’re going to start hearing about some word that ends with “-ware.” You could probably list off a few yourself, but have you ever stopped to think about why they’re all described as “something-ware?” For this week’s Tech Term, we’ll take a peek at why we refer to things that way.
Why ‘Ware?’
It does seem like a strange part of the word, unless you look back to where we get it. According to Wiktionary, Software was first coined as a term in 1953, and was named based upon the fact that the term for the physical elements of the computer were already known as hardware. A quick peek into the online Merriam-Webster dictionary gives us a few definitions for the root of that word, ware.
The ones we’re concerned with are the first and the last definitions in the first entry: “manufactured articles, products of art or craft,” and “an intangible item (such as a service or ability) that is a marketable commodity.” We can combine these to give us a fair representation of what soft-’ware’ means: “manufactured articles to provide a service that is marketable.” After all, what is a computer program, if not an assortment of code meant to complete a specific task desired by a specific audience?
The word was first coined by Paul Niquette in 1953.
Different Software ‘Wares’
As you may imagine, there are plenty of varieties of ‘wares.’ Wiktionary.org offers a pretty impressive list of software types, with names derived from ‘-ware’, including the ones that you’ve already heard about, and some that are minutely specific. We’ll go over a few of these lesser-known varieties here:
Dreamware - This software type covers those that have not yet begun development and are still in the “what if there was a software that…” phase. Many of these projects never begin development, remaining something that some software developer once dreamt up.
Trialware - This variety of software is that which is only available to the user for a limited period of time, after which it is only available in a restricted form (if at all). This can be considered the free sample of software, offering just enough to make you want more.
Crapware - You know how a new computer often comes pre-installed with programs that you have no interest in, let alone the need for? This is what is known as crapware, as it takes up space without really offering anything to you. Another four-letter synonym for ‘crap’ can also be combined with “-ware” to make another, more forceful term for this variety.
Foistware - Malware can often come bundled with other, more legitimate software titles, to be installed without the user knowing. Of course, other programs can do this as well. Foistware is the term given to these software stowaways.
Fanware - Professionals aren’t the only ones capable of writing code, and even professionals will continue their coding in their off hours. Fanware describes the products that special-interest coders write to promote that interest.
Nagware - Another version of trialware, nagware describes a software title that will interrupt a user with persistent reminders to register it. Nagware will often disable the use of the program for short intervals during use, or display pop-up dialog boxes. In essence, this kind of trialware is designed to coerce a user into purchasing the full version through annoyance.
Garageware - This is a not-so-nice term for software that simply doesn’t perform as it should or has a lot of mistakes. The name is meant to suggest that the creators were total amateurs, developing this program literally in their garage.
Again, this is just a short list of the many different software varieties out there. What other ones have you heard of? Share them in the comments!
In managing business technology, we are always talking about downtime--how expensive downtime is, how downtime hurts productivity, how there are a multitude of separate situations that can cause downtime. That kind of doom and gloom may not get you to act, but it may just put you off. Today, instead of downtime, we thought we would talk about uptime.
Uptime: The Anti-Downtime
Obviously, if downtime is something to be avoided, uptime--the reciprocal state of operations--is to be embraced. Uptime means that all of your IT is working as intended and your staff is able to produce their greatest output. At The Connection, we do what we can to avoid risk, and as a result, we typically focus on avoiding downtime and providing as much uptime as possible. The question becomes how often is your IT completely functional and working for you?
The typical business has a lot of different elements working to make up their information systems. They have servers, workstations, networking equipment, printers and copiers, and much more. In fact, if each piece of your IT infrastructure has 99% uptime (they likely don’t), what are the chances that each piece is down at the same time? Uptime as a metric actually corresponds with productivity more than any other. In fact, if someone isn’t being productive when all the IT they need and use is running effectively, they are missing an opportunity.
We work hard to ensure that uptime is maximized. We constantly monitor and manage hardware, monitor networks, and put state-of-the-art tools to work that only have one job, eliminating any downtime. That’s why it is important to define the level of success that is provided by each service and system as they are available in real-time. Think about it, if you provide an employee a workstation that routinely needs support, and another a brand-new workstation that doesn’t have any technical deficiencies, can you really expect both of them to be equally productive?
In the IT world, uptime is the goal, insofar as it gives the end user the best chance at achieving success.
How We Can Help Build Uptime
As stated above, our whole business model is based on the uptime/downtime paradigm shifting dramatically in our clients' favor. We try to accomplish this in several ways. These include:
- Hardware procurement - We attempt to set our clients up for success by offering reliable technology that will work to meet their needs 100 percent of the time.
- Professional installation - Not only will we help procure solid technology, our professional technicians will configure, test, and install all computers, include all necessary peripherals and ensure that each server and workstation has the working software necessary to provide maximum productivity.
- Bulletproof networking - Networking is a huge part of the modern workplace. We set up all wired and wireless network connections, routers, switches, and all other network related equipment to the highest standards. This ensures that data flow and network access are optimally set up and maintained.
- Remote monitoring - For information systems to maximize uptime, there have to be proactive efforts made. We remotely monitor and maintain all network attached machines, eliminating any significant downtime in the process.
- Backup and Disaster Recovery - Having a redundant and actively available data backup is proven to reduce downtime in the face of a data loss scenario.
- Help Desk - If end users have problems with their individual workstations, our comprehensive help desk service is a great resource to resolve problems and reduce downtime.
If you would like to talk to one of our expert consultants about how we can help you get control over your IT and work to reduce or eliminate the downtime your organization experiences call us with your story at (732) 291-5938.
News & Updates
Understanding IT
Get the Knowledge You Need to Make IT Decisions
Technology is constantly evolving, and keeping up can feel overwhelming. Whether you want to understand cybersecurity threats, explore automation, or learn how regulations like PCI DSS impact your business, we’ve made it easy to access clear, straightforward insights on key IT topics.
Contact Us
Learn more about what The Connection can do for your business.
The Connection
51 Village CT
Hazlet, New Jersey 07730